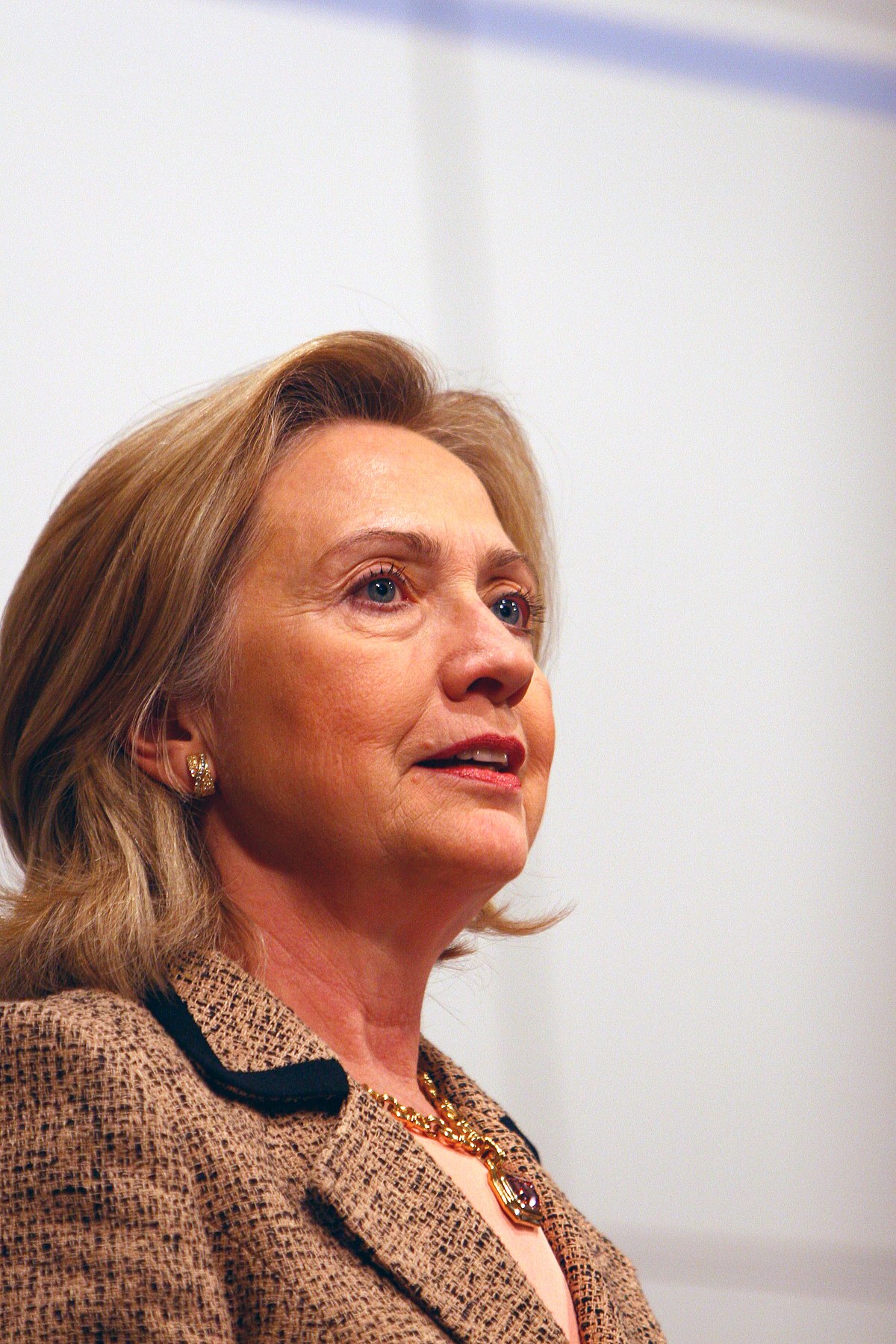
"Msc2011 dett-clinton 0298" by Harald Dettenborn. Licensed under CC BY 3.0 de via Wikimedia Commons.
Over the last two weeks, we’ve been inundated with emails and presidential candidates. I won’t spend a lot of time talking about Mrs. Clinton and what her emails may or may not contain. I could spend an entire series of blog posts on that topic. However, there are some very interesting insights this story gives us into how we perceive what security is, where we feel most secure, and whether any of that makes us more secure.
So let’s begin our discussion: NOTE: I’m no hacker or IT-guru. I’m a guy who blogs and who has a ton of opinions on this stuff. However; I’m also someone who has worked with senior-level persons and I understand how some of these components work. By no means are my opinions facts but merely points to consider.
- Security is about convenience over protection. Remember when I said “security is about peace of mind”. Mrs. Clinton decided it would be more “convenient” to send her emails (personal and professional) through a single server which she owned. Why? She reasoned, because her government-issued Blackberry could not hold more than one email account, it would be better to have a single account. Many users, especially government users, bypass existing security protocols and do and have done exactly this (except many don’t have servers at home). Does this make it right? No. The government has policies in place that state this is bad security practice and a violation of certain public records laws. Yet, ask any security professional how many times they’ve witnessed an end-user potentially compromise protective measures through circumvention out of convenience and you’ll note immediately how much their eyes roll.
- Just
because a senior-level government official is discussing something doesn’t make
it “classified information”. There’s been a massive amount of
speculation on the kind of information any investigation would turn up on Mrs.
Clinton’s servers. Like I said, I won’t attempt to go into that. However; let’s
address why we perceive there would be classified information and whether that’s
likely. Sure, being Secretary of State entails having access to some of our
nation’s greatest secrets. The job requires it. Some of that information is
considered “classified” and others not-so-much. When pieced together with other
information or on its own, that material could be extremely sensitive. The very
nature of the potential discussions
Mrs. Clinton could have had over
emails has created a great amount of concern – as it should.
Senior leaders are given amenities like secure telephone and other communication lines in their homes and offices to facilitate these kinds of sensitive discussions with “cleared” persons. In fact, during ASIS 2014, I had the great honor and privilege to hear Colin Powell speak about his time as Secretary of State. General(r) Powell recalled his final days in Mrs. Clinton’s old job and the day the Diplomatic Security Service agents assigned to him and the information technology staff left his residence while removing his secure lines from his home on his last remaining day. It should be noted Mrs. Clinton should have had the same amenities extended. As such, I’d be curious if the Internet service her server accessed did so via government-installed communication lines or privately-owned and installed lines. I digress, given the nature of what could have been discussed; it should give security practitioners who advise senior leaders on protective measures pause. - Government
computers and services are NOT intrinsically more secure. These last two
weeks, the deluge of speculation, regarding the security of Mrs. Clinton’s
email traffic being more secure had it been through government servers, has
been extreme. Seriously, have we forgotten about a number of breaches on
government email and sites in the past few years? We’ve caught hackers breaking
into NASA, NSA, the
State Department, and the Pentagon computers. Where most of this confusion
comes from is not quite understanding what having your emails on a government server
entails versus what a private (or as widely-and-annoyingly termed this week “homebrew”)
server does. People hear “government server” and they immediately conjure up an
image of a secure server with loads of encryption which would require a team of
seasoned hackers to compromise. In fact, while watching a cartoon the other day
with my son, a character brags “I hacked NORAD when I was six”. Hacking into
these systems should be a big deal because they are. However; they are not
invincible to the same kinds of human security failures and poor security
mindset when they’re designed and implemented as their commercial partners.
Your government email service can easily be hacked in the same way your private email can. Lose your credentials to log into a government computer without noticing and use a password or PIN that is easily guessed. Sadly, that happens more times than many outside of government service would ever be willing to admit. A government server does bring one thing a private server does not always – the full extent of your government agency’s information technology team, most of whom are the best and brightest at what they do and who defeat a variety of threats constantly. In other words, when a breach occurs, this team can respond immediately and use the weight of the government to mitigate the breach. Mrs. Clinton knew this, yet felt she and her staff could do better. Given what little we know of what could have been breached or whether a breach even occurred, this could have been true. That being said, it doesn’t make any of her decisions right. - The extent of how much protection to provide sensitive information disclosure is not up to the user but those who have the designated expertise within the organization. Mrs. Clinton, while acting as Secretary of State, had every right to make her own determinations regarding how her agency would protect sensitive information to some extent. That did not provide her with any right to decide, without consultation or coordination with her information security staff at the State Department, to forego policies she enforced on her subordinates. It is highly doubtful Mrs. Clinton would have absolved a junior-level employee who would have been caught in a sensitive information breach from their personal email account. No, we all know she would have directed her staff to punish them. However; the implied arrogance to believe you can enforce one security policy meant to mitigate vulnerabilities and lessen risk while ignoring your own failure in abiding by those very decrees, is striking, to be honest.
- Politics
obscures our ability to ascertain the more important security issues in crises
like these. Mrs. Clinton’s enemies are clamoring to be the first one to
hand her an indictment or hold her letter detailing her retirement from
politics. While that is unlikely, it seems to be a centerpiece in most
political discussions regarding the emails. Most of this is centered around the
potential for classified information
being on the servers. Again, this is unlikely, given we still have zero clue about what’s on the server.
What have not been discussed are the very relevant questions pertaining to total protection and mitigation. No one has addressed to any significant degree whether Mrs. Clinton is the only Cabinet member to have done this (she isn’t) and whether she received advice from her designated State Department IT staff (I’m betting she didn’t and relied on her political staff’s IT department who are not government employees). I’d also be curious whether the Secret Service devotes any time to protecting their protectees online as well (doubtful and perhaps an area to pursue). How many people had access to her server? At what level were they cleared? This is important because in order to read unclassified emails which contain “For Official Use Only” you need to be a “cleared” employee. Very few people are asking these questions but should.
Does any of this make us safer now that we know? In some ways? Yes. In others? No. Mrs. Clinton’s emails crisis occurred for a variety of reasons. Many of those were aggravated because she is a political entity at her core. She may have felt as though having a server she owned she was more “secure” from some threats of the political variety. While it is always good to protect yourself from threats, one should not forget the more likely and persistent threats which are present because of the job you hold. She lost sight of that and ultimately forwent some very sound security practices. Then again, she may have well had a number of mitigation measures in-place. Unfortunately, we may never know what they were and thus remain a bit unsure of our protection.