Saturday, November 29, 2014
The GateShack - Episode 04 - Ferguson - Lessons Learned
Show Notes:
First, I’d like to extend an apology for the previous episode’s audio issues. I was attempting something new while preparing the podcast and it backfired on me. For that, I apologize and I appear to have the sound sorted out.
During today’s podcast, I wanted to continue our discussion on Ferguson with some of the lessons we’ve learned since August. I focus a lot on some of the mistakes made by Ferguson PD during the early days of the protests. Some of those mistakes are still being made and they offer insight into how we, as security and law enforcement officers, can do better when responding to civil disturbances. Feel free to leave a comment on Twitter using the hashtag #FergusonLessons or leaving a comment below.
Wednesday, November 26, 2014
Tuesday, November 25, 2014
Riots: The Physical Security Considerations
 |
| LONDON, ENGLAND – AUGUST 08: A rioter throws a rock at riot police in Clarence Road in Hackney on August 8, 2011 in London, England. (Photo by Dan Istitene/Getty Images) |
Last night, riots erupted all over Ferguson, MO after the grand jury announced they would be declining to indict Darren Wilson, the police officer who shot and killed Michael Brown. This post isNOT about that decision or the investigation itself. My opinions on that will remain out of the public sphere. However, I would like to discuss the unique physical security considerations mass protests and riots present for security practitioners. I’d like to discuss what those challenges are and how we can counter the physical attacks against assets during these events.
- Protests are extremely dynamic and what looks peaceful five minutes from now could be a full-blown riot the next. People assume they can do a lot of things they simply can’t. Predicting the actions of hundreds of people and whether they view your assets as a legitimate target is one of them. This is almost impossible to do. So don’t. Just err on the side of caution and just assume your assets are.
Social media and the news can lull practitioners into believing the intelligence they’re receiving about the threat is accurate. In many cases, it can be. However, you should never use anyone else other than yourself to determine how a crowd will behave and view your assets. - Agitators carry an assortment of tools to target your assets. Just because you’re seeing rocks and water bottles being thrown now does not mean you’ll only see that as a weapon against your assets. They may use chainsaws, bats, pipes, bricks, Molotov cocktails, guns, etc. against you and your assets. Consider the full gambit of tools they will have access to, factor in the time they have had to pre-stage gear, and experience. Make sure your preparations are comparable for probable threats.
- The people protesting aren’t always your biggest threats – they can also be your savior. In many cases, as we saw in August and last night, bystanders and peaceful protesters stood up to defend local businesses in Ferguson. Most of those storefronts were businesses who had made in-roads with protesters beforehand. Also, the peaceful protesters realized their protest was being hijacked by anarchists and thus, losing the narrative. Because of this, many protesters actively protected storefronts. You should make every effort to reach out to protesters beforehand. In some cases, I would consider offering a reward for any protester caught seeing defending your assets.
- Some storefronts are targeted not because of who they are but for what they have inside. Last night, I advised any pawnshop owner to remove all weapons from their locations. Why? Because most physical security measures used to defeat thieves is usually meant for one or two persons attempting the threat and reliable police response. As last night proved, the police will be to busy with other response to ensure adequate protection to those stores. If you can’t move the guns, then remove their firing pins and ammunition immediately. If you have some clue that rioting could occur, you owe it to yourself and the community you service to at least remove the weapons or firing pins until you know for sure the threat is gone.
- Consider how we’re trained as professionals to protect assets in your riot contingency. We detect, deter, delay, and if necessary, stop the threat. Are the measures you’re implementing do that? Can they do that with a crowd amassing your facility? If not, can you afford the risk of failure?
- Remove any weapons or explosive materials from stores.
- Shutdown gas station pumps.
- Consider constructing steel shutters or a roll cage around your storefront. The shutters and roll cage should be secured with a heavy-duty lock with a buried shackle to prevent cutting it or using a shim to pick it.
- Install heavy-duty glass or board windows from the inside and outside.
- Remove cars from parking lots to other secure areas. If this is not possible, consider erecting a larger fence where the top is bent facing towards the adversary. This configuration is used in prisons to prevent scaling which is difficult to do for most people. A ladder is required in most cases. Also, remove those assets closest to the fence.
- Conduct counter-surveillance daily before the protest is said to occur. Be on the lookout for any suspicious behavior. Have you noticed new people around your stores you haven’t seen before? How much loitering occurs and is any of it out of the ordinary? Are people asking strange questions about when you typically shutdown for the day or when do you “really lock the doors”? Have your loss prevention guys noticed any increased observance of camera locations?
- Barriers. Use them. I can’t say this enough. When I was a young Airman, barriers were a part of my everyday life. We used them a lot for increased threat mitigation, civil disturbance, crowd control, and even presidential visits. My preference is for the plastic jersey barriers to be filled with water or sand. Water should be used in winter because it’s more likely to freeze than like, unlike in summer where it tends to so a lot. Jersey barriers, when not filled, are highly mobile and allow the practitioner flexibility in how, when, and where they can be deployed. In many cases, a pick-up and a few able-bodied people is all you need to move them, where concrete and sandbags require forklifts and more bodies.
- Fences. Put them up. You should make every effort to ensure protesters will have to struggle to get to your assets. The cheapest and best way to do that is through proper fencing. You should install a fence typically around 10 to 15 feet and weigh whether or not your insurance can handle barbed wire. Another consideration, if you’re using barbed wire, is aesthetics. Can you do business with the barbed wire on the fence? Some customers respond differently to that.
- Consider guards if you have no other choice. Seriously, don’t hire guards if you don’t need to. Security officers are great at what they do. If the target of the protests is law enforcement, who do you think the rioters will look at as a potential target? Those stores with guards in uniform. Not saying you shouldn’t use guards but understand their risk and that they don’t always lower your threat profile.
- Don’t get political. Seriously, if you have a Twitter profile for your store and you’re talking about how you hate the protesters all the time, you’re making yourself a larger target. That’s what we call “begging for a fight”. Stop. Instead, talk about how many people in the community you employ, how long you’ve been there, and how the damage impacts you and other businesses. Stay away from any discussions about what is being protested.
Monday, November 24, 2014
The GateShack - Episode 02 - The Myths of Security
During today’s episode, I cover the major myths about security and the ramifications for ignoring them. We’ll also explore Mubin Shaikh’s book, Undercover Jihadi: Inside the Toronto 18 – Al Qaeda Inspired, Homegrown, Terrorism in the West
Show Notes:
Mubin Shaikh’s book - Undercover Jihadi: Inside the Toronto 18 – Al Qaeda Inspired, Homegrown, Terrorism in the West
For more information on Geofeedia, visit http://www.geofeedia.com
Tuesday, November 11, 2014
The GateShack: Episode 01 - Getting The Semantics of Security Wrong
Monday, November 10, 2014
The 41 Security Tweeps To Follow Today
Sunday, November 9, 2014
Tuesday, November 4, 2014
Monday, November 3, 2014
VIDEO: Elevator Hacking: From the Pit to the Penthouse by DeviantOllam
From the video’s description:
Throughout the history of hacker culture, elevators have played a key role. From the mystique of students at MIT taking late-night rides upon car tops (don’t do that, please!) to the work of modern pen testers who use elevators to bypass building security systems (it’s easier than you think!) these devices are often misunderstood and their full range of features and abilities go unexplored. This talk will be an in-depth explanation of how elevators work… allowing for greater understanding, system optimizing, and the subversion of security in many facilities. Those who attend will learn why an elevator is virtually no different than an unlocked staircase as far as building security is concerned!
While paying the bills as a security auditor and penetration testing consultant with his company, The CORE Group, Deviant Ollam is also member of the Board of Directors of the US division of TOOOL, The Open Organisation Of Lockpickers. Deviant runs the Lockpicking Village with TOOOL at HOPE, DEFCON, ShmooCon, etc, and he has conducted physical security training sessions for Black Hat, DeepSec, ToorCon, HackCon, ShakaCon, HackInTheBox, ekoparty, AusCERT, GovCERT, CONFidence, the United States Military Academy at West Point, and the United States Naval Academy at Annapolis. His favorite Amendments to the US Constitution are, in no particular order, the 1st, 2nd, 9th, & 10th.
Howard Payne is an elevator consultant from New York specializing in code compliance and accident investigations. He has logged over 9,000 hours examining car-tops, motor rooms, and hoistways in cases ranging from minor injuries to highly-publicized fatalities, and has contributed to forensic investigations that have been recognized by local, State, and Federal courts. Howard has appeared on national broadcast television making elevators do things they never should. When he’s not riding up and down high-rise hoistways, he moonlights as a drum and bass DJ and semi-professional gambler. His favorite direction is Up and his favorite elevator feature is riot mode.
Sunday, November 2, 2014
Saturday, November 1, 2014
Thursday, October 23, 2014
OPINION: What The Ottawa Shootings Can Teach Us About Social Media As a News Source
I have been on social media for a LONG time. In the time that I have been online, I have taken part in real-time discussions and analysis for a variety of events in the security “lane”. I’ve talked about an assortment of events ranging from Dorner to the Ottawa shooting. Each time, I’m astounded by how fast the events that transpire are posted in almost-real-time. The advent of the Internet and the smart phone has made all bystanders on-scene correspondents and social media users like myself the most sought-after “experts”. I argue, therein lies social media’s greatest drawback during these events.
- We get stuff wrong a lot. Yesterday’s shooting highlights some of my frustrations with social media as a news sources. On more than one occasion, various sources posted certain information as vetted “facts”. Most of those reports were false and depicted a scene far more chaotic than the one that was occurring. Why? For a lot of reasons – some of which I don’t have enough space in this forum to adequately articulate. Chief among them – confirmation bias. Many of us were simply re-posting information that solely confirmed what we either wanted the scene to be or the headline struck an emotional chord. Worse than that is another reason not related to confirmation bias but perception bias – some people re-posted information because it supported a prejudice or a political ideology.
- We ignored the danger of “first reports”. I have but one cardinal rule with social media as a news source remember ALWAYS “first reports” are wrong. Seriously, the first eyewitness accounts from a major incident will almost surely be wrong. Why? Because eyewitnesses suck. No two people in an attack ever see the same thing and their perceptions will also be markedly different. The folks at the Innocence Project do “yeoman’s work” on this very issue for their clients. I HIGHLY suggest we all read up on their work to understand why we shouldn’t always trust unconfirmed eyewitness reports.
- We created confusion in order to stay relevant. That sounds harsh and mean. Hear me out. With some of us having “followers”, during an event like Ottawa or Dorner or Boston, it is very tempting to believe we either need to share information which has already been posted several times over or comment on that information before they can be vetted in order to appear on top of things. Instead, we should wait until the information can be verified and is still relevant to events happening in the present. These events can be confusing and there is no need to add to the chaos and potentially colour the situation in a way that is not accurate. Our time to pontificate on the events can come later.
- We confuse hazardous behavior with context. I get it. The bullets are flying and you want the entire world to know. I get it. Your shot could be the one that depicts the essence of the event. I want you to get that shot. I also want you to be safe and not to place first responders in jeopardy. STOP POSTING LOCATIONS OF YOURSELF AND OFFICERS RELATIVE TO THE SHOOTER AND WHAT YOU’RE HEARING VIA POLICE SCANNERS. Guys, I was a 911 dispatcher many moons ago and I’ve worked in a security and law enforcement for over a decade. If there’s one thing I know from my career, law enforcement operations can be extremely difficult for even seasoned pros to decipher and scanners are not always a good place to get an accurate account of what’s happening. A cop responding to a shooting is just a cop responding to a scene. If he hasn’t verified a shooting took place, a shooting hasn’t taken place.
- We assumed shooter counts and body counts were accurate. There are few things that can either mellow people out or cause even more chaos on social media than body and shooter counts. During the Ottawa shooting, the number of shooters originally accounted for by social media was up to FIVE with a couple of shooters on roofs. That depicts a much different scene than the one we later found to be true of one shooter who was shot and killed inside a building. Keep in mind, law enforcement would only confirm initially one shooter in the beginning, yet somehow there was five. How did that happen? It happened for all of the reasons I’ve talked about in this post and one that is far more dangerous.
- We believed people with “sources close to law enforcement”. Nothing makes me cringe more than hearing “The police confirmed XYZ” from a person on social media only to learn the source cited as “the police” was cited by the media as a “source close to law enforcement”. What does this mean if not “the police”? It simply means two things – either the source is a cop who is giving out information to the press without authorization or it’s someone the media knows is not a cop and your knowledge of that truth could diminish how you view the accuracy of the source. A perfect example of the latter is a cop’s wife or an intern at the police department. They both have access to insider information but neither of them are actually investigating anything. There is also another reality – the “source” could also be made up. No matter how bad the sourcing could be, I grow disheartened more and more as we accept this as a set of reliable information to base opinions and reactions to.
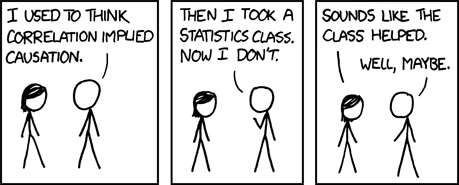
THIS. Read and heed!! pic.twitter.com/hSwE5LeKRi
— Scriven King (@scrivenlking) October 23, 2014
Tuesday, October 21, 2014
Monday, October 20, 2014
The “Rules” From 1829 Which NYPD Commish Bratton Carries
In 1829, Sir Robert Peel, upon founding the Metropolitan Police in London (the world’s first recorded organized police force), believed certain principles would guide his department into being professional and accountable. There were various attempts at policing before but none had ventured to be as organized as Peel’s was. While “the Met” is the first organized and officially sanctioned police force in the world, many officers are unaware of who he is or the principles he founded modern policing on. As events continue to occur which cause the public to question the professionalism and accountability of its police officers, I HIGHLY suggest any student of criminal justice and policing read these principles and determine whether their respective police departments still adhere to these principles or if they’re mere guides.
Principle 1 – “The basic mission for which the police exist is to prevent crime and disorder.”
Principle 2 – “The ability of the police to perform their duties is dependent upon public approval of police actions.”
Principle 3 – “Police must secure the willing co-operation of the public in voluntary observance of the law to be able to secure and maintain the respect of the public.”
Principle 4 – “The degree of co-operation of the public that can be secured diminishes proportionately to the necessity of the use of physical force.”
Principle 5 – “Police seek and preserve public favor not by catering to the public opinion but by constantly demonstrating absolute impartial service to the law.”
Principle 6 – “Police use physical force to the extent necessary to secure observance of the law or to restore order only when the exercise of persuasion, advice and warning is found to be insufficient.”
Principle 7 – “Police, at all times, should maintain a relationship with the public that gives reality to the historic tradition that the police are the public and the public are the police; the police being only members of the public who are paid to give full-time attention to duties which are incumbent on every citizen in the interests of community welfare and existence.”
Principle 8 – “Police should always direct their action strictly towards their functions and never appear to usurp the powers of the judiciary.”
Principle 9 – “The test of police efficiency is the absence of crime and disorder, not the visible evidence of police action in dealing with it.”
Sunday, October 19, 2014
OLD SCHOOL SATURDAY – THIS DUDE IS THE COOLEST NARC YOU’VE EVER SEEN
This has to be the coolest undercover cop/narc I’ve ever seen in my life.
An undercover police officer on duty in the 78th Precinct in Brooklyn. July 1, 1969. pic.twitter.com/WULZ02e36q
— Historical Pics (@HistoricalPics) July 15, 2014
OLD SCHOOL SATURDAY – VIDEO: STAY ALERT, STAY ALIVE – THE TECHNIQUES AND MECHANICS OF ARREST
From the video’s description on Amazon.com:
A law enforcement training film on how to safely and efficiently arrest criminals. Includes dramatizations of what happens to unwitting officers.
CARTOON: FEAR IS THE ENEMY’S GREATEST FORCE MULTIPLIER
This is picture conveys a lot of what I’ve been preaching tweeting about our reactions to Ebola. Most of it has been incredibly ridiculous which provide interesting challenges for those of us in security. While fear drives much of security, it also can create obstacles around measures meant to protect and successfully mitigate threats.
Not the virus...the effect of fear from it on the people...coming soon @JNathaniel7: #Ebola http://t.co/SswUszqYjE
— Kristina Dei (@2kdei) October 19, 2014
Thursday, October 16, 2014
How-To: Map Ebola Like A Pro In Ten Easy Steps
‘The Problem
With countless agencies now operating in Africa to combat Ebola’s consistent climb upwards, medical personnel operating there are finding out they face unique challenges in Africa. I experienced much of what they’re going through while stationed in Korea my first tour as a security advisor and driver. At the time, the biggest obstacle I faced was getting around Seoul. While I had the benefit of transliterated maps, I would have killed for a GPS unit. Relief workers in Africa are facing a similar dilemma. Most people don’t realize how much of the African urban and rural settings are not mapped. There are entire road networks and villages no map has officially recognized. In a situation where you have to make contact with every single potential victim, being able to safely navigate to them is paramount.
The Solution
So how do we make sure we have the areas are mapped? Well, by way of open source mapping. In other words, citizen volunteers sit at computers and outline and label every nuance of interest to aid organizations. Once the citizen volunteers do their part, validators spot-check your work and send off the information you collected that was accurate and send back anything you sent off that was wrong. In the entire timeframe of instruction to operation, I mapped over 17 buildings and a few roads. Shortly before writing this post, I mapped 7 roads and 3 foot paths. Total time to do all of this was roughly 30 minutes with only an hour and half worth of instruction. Most importantly, the software this is done on is free and open-source.
How-to
I know you’re curious how you can do the same thing. At least you should be. If you don’t think you should be, call me and I’ll explain rather vigorously. So here’s how to get started.
- Go to http://www.openstreetmap.org and sign-up for an account. Once your email is confirmed, then follow Step 2.
- Go to http://task.hotosm.org to see the open tasks for humanitarian groups working on Ebola.
- Before accepting any tasks, I HIGHLY suggest you go to http://wiki.openstreetmap.org and read the articles on how to navgate and what exactly the various terrain feature labels correspond to visually on a map.
- Once you’re done there, go back to http://task.hotosm.org and find your tasks.
- Click on the task you want and then go to the side map and click on an are that is not “done” or “validated”. It should be the grid with no coloring. Once you click there, look to the left sidebar and you should see where it says start mapping, click there.
- Next, click on the arrow next to where it says “Edit with” and go to iD Browser. Trust me, you’ll thank me later.
- From there a map should have opened up in another browser where you will do your edits.
- Find your area and zoom in on areas where there’s a lack of data and outlines are not done for features.
- Click on either the line or poly pointers at the top menu bar and then outline the shapes of what you’re tasked. When done, click on the last point of the shape again. If necessary, click on any line in the shape to bring up a mini-menu that will “square” edges away.
- When you feel like you’re done, click on the save button at the top menu bar. Feel free to leave a comment in the sidebar. I was told to put “task-whatever the number was-hotosm – whatever feature the task called for” Go back to original hotosm screen and make sure you “unlock” this map so others can work on it. Before you unlock, be sure to leave a comment stating what you did.
http://wiki.openstreetmaps.org
http://www.openstreetmap.org
http://mapgive.state.gov
http://task.hotosm.org
That’s it. Easy peasy. By the end of the day, you will have helped out relief efforts in perhaps one of the biggest public health crises the world has seen in a while. Give it a whirl and let me know what you think. Also, share this information with other people.
Thursday, October 9, 2014
LIST: A Few Good “Official” Ebola Resources
As an ongoing effort to disseminate objective information to my readers, regarding Ebola, I’ve decided to put together a list of sources I consider minimally unbiased who have the data to give security practitioners an idea of how the outbreak is progressing. NOTE: I REALIZE THIS LIST IS NOT ALL-INCLUSIVE. THESE ARE MERELY SOURCES I THINK ARE IN THE BEST POSITION TO DELIVER OBJECTIVE DATA AND ALLOW FOR SECURITY PRACTITIONERS TO MAKE THEIR OWN ANALYSIS.
- CENTER FOR DISEASE CONTROL EBOLA PAGE – http://www.cdc.gov/vhf/ebola/
- CDC – WHAT’S NEW PAGE – http://www.cdc.gov/vhf/ebola/outbreaks/2014-west-africa/whats-new.html
- CDC COUNTS – http://www.cdc.gov/vhf/ebola/outbreaks/2014-west-africa/case-counts.html
- CDC – WHAT THE CDC IS DOING – http://www.cdc.gov/vhf/ebola/outbreaks/2014-west-africa/what-cdc-is-doing.html
- CDC – COMMUNICATION RESOURCES – http://www.cdc.gov/vhf/ebola/resources/index.html
- WORLD HEALTH ORGANIZATION EBOLA PAGE – http://www.who.int/csr/disease/ebola/en/
- WHO EBOLA MAP -https://who-ocr.github.io/ebola-data/
- DEFENSE THREAT REDUCTION AGENCY – http://www.dtra.mil/
- GOVERNMENT OF LIBERIA EBOLA PAGE – http://www.micatliberia.com/index.php/ebola-update.html
- MONROVIA – US EMBASSY – http://monrovia.usembassy.gov/
- DOCTORS WITHOUT BORDERS – http://www.doctorswithoutborders.org/our-work/medical-issues/ebola
- NGOs Responding To Ebola – http://www.cidi.org/ebola-ngos/#.VDbCyWddXTo
Wednesday, October 8, 2014
REPORT: Police Under Attack – The Police Foundation Review of the Christopher Dorner Incident
When I mention the name, Christopher Dorner, among my friends in law enforcement, the mood changes dramatically. I know I will never forget the day he attacked his fellow officers and their families. I have spoken at great length here about Dorner, so I won’t waste more of your time talking about him. However, I did find the following report published by The Police Foundation. If that name sounds familiar, it should. These were the folks behind the Kansas City Police Patrol Experiment. Recently, the published this report detailing a lot what happened during Dorner’s attacks. For civilians, it’s an after-action report of sorts. I HIGHLY recommend reading it.
Tuesday, October 7, 2014
OPINION: The Fine Art of Failing vs Mitigating in Security
Last week, I wrote a post regarding “security myths”. In that post, I was hesitant to be overly critical of the United States Secret Service’s response to recent intrusions. In the days following my article, there have been very illuminating leaks regarding exactly what happened that day. One revelation was the intruder actually made his way inside the White House. Before the leaks, I stated whatever the After Action Reports revealed; the entire incident was not a mission failure. I stand by that conclusion for a few of the reasons outlined below:
1. Mitigation is the goal of any security program. The idea that we, in security, prevent bad things from happening is a huge myth. You can lock your doors and windows to thwart bad guys but the only people who make the final determination whether the bad guys continue are the bad guys. We mistakenly believe security is a physical entity we can see, when in fact, it is a psychological construct designed to enable us to move on from our fears to do other important things vital to survival. What we seek is protection which is only achieved by mitigation. Mitigation is what we do to reduce the potential harm inflicted on us if the adversary should show up. So the lock does not prevent crimes but its presence gives us some sense of security, while it also mitigates potential threats that may come via the doors.
Prevention is perhaps the one thing we don’t control but assume we should. In the case of the Secret Service, yes, there were lapses in security. Uniformed personnel were obviously not able to sufficiently cover the grounds of the White House. They could have done more to secure the doors and should have posted someone able to engage a threat coming for the North Portico doors. Someone at Secret Service did on multiple occasions succumb to allowing convenience to overrule the imperatives of adequate mitigation. The White House staff and the United States Secret Service did fall for the psychological trap of security, instead of following a plan that guaranteed mitigation.
Feeling safe is not the same as being safe. That being said, various mitigation tools did work like the successful evacuation of the press and staff who were in danger. Also, an off-duty agent was successful in aiding in the apprehension of the subject. It’s important to note the Secret Service’s mission is to protect the President and Vice President as well as all principles designated by law. In short, with no loss of life, this mission was accomplished solely because other mitigation tools had a chance to do what they were designed to do. It was a mess and it certainly does not reflect well on the Secret Service.
2. Prevention as a security goal and task are unrealistic. An old adage I remember from my days in the Air Force is “the enemy gets a vote”. No matter how good your plan is or how great your mitigation tools and techniques are, nothing you do will prevent the enemy from doing anything except killing him. Detention is, at best, only guaranteed to delay their actions. In fact, the only reason I believe the saying “Only you can prevent forest fires” is because I always thought Smokey the Bear was talking to potential perpetrators of forest fires and not victims. So why do we insist on believing prevention is realistic, if we’re solely addressing victims? What most people want are more effective mitigation tools but assume the semantics mean the same when they don’t.
3. Every security organization is bound by the use of force continuum. Some argue the Secret Service should have killed the subject immediately. Many of these people ignore Graham vs Connor which dictates the level of force an officer can use against any subject. That standard is called the “objective reasonableness standard”. This comes from the idea an officer can use whatever force is necessary to stop any threat as long as that force is comparable to what a reasonable officer would deploy in similar circumstances. Would a reasonable officer shoot a potentially unarmed man just because he committed a trespass violation? Imagine the precedence we could set by implying under certain circumstances it is reasonable to kill someone for seemingly minor offenses. Does a simple trespass have the potential to be more at the White House? Oh, for sure. Until a person displays a lethal “intent, opportunity, and capability” against another, we are bound to use the force a reasonable officer would to stop the threat. Otherwise, we stand the chance of the White House become a favorite spot for those looking to die via “suicide by cop” or placing the White House and its security at the center of a potential tragedy.If these statements make you upset, then I implore you to read what I said again. I never said deadly force was not authorized. It is. Deadly force can be used as soon as the threat meets those three criteria I established prior.
4. Like it or not, the White House is a tourist attraction and that complicates things greatly. Did you know the White House receives millions of visitors annually? This accounts for those who merely gaze through the fence and those who come to take a tour. In partnership with the Park Service, the United States Secret Service is tasked with protecting the White House in spite of the enormous opportunity various threats have to carry out an attack either against the throng of tourists or the President. In most executive protection assignments, the principles address is a matter of neither public record nor access. The Secret Service is in the unenviable position of protecting the President in a vastly different environment. Measures we’d like to see taken in one regard (i.e. fortifications) which help mitigate the visibility of the grounds and the principles are often not what the public envisions when they come to see their “house”.
5. In some executive protection circles, if not most, there is a delicate balance between protection and convenience. Most people who have never worked an executive protection detail don’t get how often the people protecting dignitaries are overridden when it comes to matters of convenience. I have known a many of personal protection officers who have complained they have been told to “stay with the car” when a VIP goes some place where his protection details has no visibility.
With the White House incident, we learned a key mitigation tool was rendered ineffective because the White House Usher’s Office decided the intrusion notification system was too loud and needed to be turned off. In a world where one sees protection and is lulled into feeling “safe”, this is an easy mistake to make. It never costs you in the short-term. It won’t hurt today but you can bet when the adversary shows up, you’ll wish you had that mitigation tool in place. Is this a fault of the Secret Service? Sure, in some ways. They could have pressed the issue and said “no”. They, not the Usher, are legally mandated to protect the President. If that tool aids them in doing so, then the tool stays. Period. Is there a culture in Secret Service that enables this? I don’t know. What I can tell you is there is a culture in DC and the White House that does. Hopefully, the hearings which are going on will further highlight the need to silence the parts of that culture that negate sound protection practices.
6. Finally, stuff just happens. During my 14 years in this industry, I spent 10 in the service of the United States Air Forces in military law enforcement and security. My first few years were spent as a young Airman performing what is commonly termed as “gate guard” duties. I stood at the main gate of our installation controlling entry and exit. I was also responsible for issuing countless visitor passes. I was really good at my job. So good that I was winning awards and accolades above my peers. However, on one fateful day, I encountered something no one expected.
A female Technical Sergeant and her male guest came to the visitors’ center looking to get a visitor pass. All that was required at the time was a military ID card from her and a government issued ID from him. I checked his ID which was a passport and noted all of the details had matched. Our conversation was good and I detected nothing extremely peculiar. Actually, I did note something but I was stationed in Idaho so it was not a big deal at the time. Her guest asked if he could bring his personal weapon on the base. I told him he could not and asked if he had the weapon. He replied he hadn’t and she reassured me he hadn’t one. The question seemed one of mere curiosity in an attempt to make “small talk”. I had done everything I could do at that moment.
It was not until two days later was I approached by our investigators and several federal agents informing me several tactical vehicles were coming to apprehend him for being a fugitive – he had killed several people and almost killed a police officer. I was crushed. How could this happen? Should I have asked more questions? Would they blame me?
Years later, still torn by this, I asked a mentor who informed me I had done nothing wrong and in fact did everything right. Despite my best efforts, the adversary won. This is an unfortunate but inherent ingredient of protection. No matter what you do, the enemy will still do what he does and it is your job to prepare for that and win.
6. Finally, stuff just happens. During my 14 years in this industry, I spent 10 in the service of the United States Air Forces in military law enforcement and security. My first few years were spent as a young Airman performing what is commonly termed as “gate guard” duties. I stood at the main gate of our installation controlling entry and exit. I was also responsible for issuing countless visitor passes. I was really good at my job. So good that I was winning awards and accolades above my peers. However, on one fateful day, I encountered something no one expected.
A female Technical Sergeant and her male guest came to the visitors’ center looking to get a visitor pass. All that was required at the time was a military ID card from her and a government issued ID from him. I checked his ID which was a passport and noted all of the details had matched. Our conversation was good and I detected nothing extremely peculiar. Actually, I did note something but I was stationed in Idaho so it was not a big deal at the time. Her guest asked if he could bring his personal weapon on the base. I told him he could not and asked if he had the weapon. He replied he hadn’t and she reassured me he hadn’t one. The question seemed one of mere curiosity in an attempt to make “small talk”. I had done everything I could do at that moment.
It was not until two days later was I approached by our investigators and several federal agents informing me several tactical vehicles were coming to apprehend him for being a fugitive – he had killed several people and almost killed a police officer. I was crushed. How could this happen? Should I have asked more questions? Would they blame me?
Years later, still torn by this, I asked a mentor who informed me I had done nothing wrong and in fact did everything right. Despite my best efforts, the adversary won. This is an unfortunate but inherent ingredient of protection. No matter what you do, the enemy will still do what he does and it is your job to prepare for that and win.
Monday, October 6, 2014
VIDEO: Microsoft CSO, Mike Howard, Talks The Benefits Of ASIS Members
This video is a bit dated (recorded in January) but what Mr. Howard says here is absolutely correct. I can attest to this, firsthand. You could say this blog wouldn’t be here for you to read, had I not discovered the American Society for Industrial Security, International. Approximately 10 years ago, I joined ASIS seeking out people who were motivated like me and who enjoyed doing physical security. I thought the people I would meet would be, at best, middle management security guys/gals. Was I surprised! I met folks from all over security and was involved in doing things like volunteer site surveys which my chapter did for a nature reserve looking to upgrade their security. This was way above my pay grade, you can say. Exposure to activities like this and the people ASIS has in its ranks, motivated me to start this blog, in an effort to educate my troops and the general public about security. The rest is history. I HIGHLY recommend you to consider joining ASIS immediately.
Monday, September 22, 2014
OPINION: Top Eleven Myths Supporting Security Critiques
Well, this seems to be the season for "major" security breaches. There seems to never be a week in the last few months some retailer or government entity isn't revealing how it's been penetrated. Along with those revelations comes the torrent of critics who ask "How could this happen?" and proclaim "This is the worst thing ever!....Incompetence!....This is epic!" Please, note the heavy amount of snark and sarcasm there. As one of a few people who sort of gets security, I often find myself getting increasingly frustrated about the growing number of amateur critics who have in some way implied "expertise" on a topic few professionals in the industry actually get. So in an effort to educate everyone and to vent (okay, mostly to vent), I've decided to do a piece on the myths surrounding security. Bear with me. If it feels like I've kicked you in your stomach, good - that's why I'm doing it.
- Physical security is easy. Sigh. This is the most upsetting and doggone frustrating statement a security professional could hear. Contrary to popular belief, security is not easy. It's pretty hard, actually. There's a lot more that goes into security than just bag searches, menacing guards, cameras, and alarms. It encompasses multiple disciplines which contribute to the security mission. They range from everything from the information security to operations security to risk management to executive protection to physical security to personnel security to personal security. All of them bring something unique to the table. Each is an integral part of the total security package. It takes a professional versed in all of them to be able to deploy the package seamlessly.
- Anyone can do security. Ugh. Wait, no. Double - ugh!! Not everyone can "do" security. As I stated before, it's hard. It's not rocket science but if the only thing you've ever protected in your life was a bike in a bad neighborhood, you may not be as qualified as you think to speak expertly on matters such as the security surrounding rather complex and sensitive facilities as the White House or military bases. I know I just made a lot of folks in the DC press conglomerate very unhappy. So let me explain. You can have all of the facts on an issue but still not get the nuances behind how to properly execute an effective security plan or understand the stark realities those facilities face. As a matter of fact, there are people in the job who barely get some of these concepts which explains why so many security plans fail.
I've been in this industry for 14 years and there are things I'm learning every day. I am no "expert" and I often eschew any effort to attribute me to that title. It is also my suggestion, given my background, if I admit to knowing far less than most "experts" with less experience are willing to, then maybe you should be questioning their "expertise" as well. Think you can "do" security? I'd happily place you in charge of physical security at the White House which receives MILLIONS of visitors every year and hosts the most targeted human being on the face of planet Earth. Good luck. - There's entirely too much security for this. Another sigh. Seriously, folks. Unless you've walked in the shoes of the person who designed the security apparatus for that facility or worked in a similar post, you may not understand the thought-process behind how security is set-up there. In order to better educate most folks who are not familiar on this topic, I'll take a moment to digress and speak on the mission of security and how it is often set-up.
Security's primary mission, no matter the discipline, is pretty much the same minus some semantics. It is to detect, deter, delay, and destroy. There are professionals who will undoubtedly find issue with my choice of words here. My message to them is clear - I get it but let's think more figuratively. While it is optimal in security to see the threat before he arrives, that may not always be the case. In fact, there is very little empirical data to suggest much of what is done in physical security actually deters the truly dangerous threat. However, what is quantifiable is delaying and subsequently disrupting or destroying the threat's ability to continue their actions.A great example of classic defense-in-depth
Finally, let's examine what drives most security plans. Much earlier, in another post, I wrote extensively about risk management which is a process by which security professionals and their stakeholders ascertain the level of risk they're able to maintain and the mitigators they plan to deploy minimize the risk. As you can imagine, this process is what most security plans are derived from. Within those plans, therein lies the basic outline of how most modern security is implemented - defense-in-depth. This is best explained by asking you to imagine an onion. As you peel the skin on any onion, you'll note the various layers contained. Security is much like that. Every protected resource has an outer layer of protection which supports the inner layers. The close you get to the resource, the more intimate the security. Imagine the White House. The far most outer layer of security there could be the scores of CCTV systems found all over the DC area. From there, the security mechanics become more intimate with their resource. Stop laughing. I hear the jokes. Serious. Stop it. The inner layers encompass a new level of protection more closer to the resource than the next. See, I cleaned it up for you. - The security guys just need to do a better job. Really? Like seriously. What qualifies you to make statements like that? Have you examined the actual, no-kidding threat intelligence or data to understand the nature of the adversaries those "security guys" may face or the countless attacks which get thwarted. A great example of this is a conversation I had recently with a political website editor regarding how the United States Secret Service would be better served by doing a "better job of managing its fence" rather than deploying checkpoints further from the ones already at the gates closest to the White House. I strongly disagreed not because I love checkpoints (I don't - see my thoughts on crowds) but because I understand (because I've actually done executive protection and physical security versus offering critiques about something I only read about) what drove the US Secret Service to acknowledge they were considering checkpoints. You would be remiss as a professional not to consider them as an option. I think we would all do a lot better to understand the difference between a consideration and an implementation.
- I have a PhD so I have the magic ability to know all things related to security, though, my PhD is in an unrelated field or I've written books non-security professionals think is dope. I won't waste a lot of time and space on this but this is a growing issue throughout social media. Stop it. There are few things more irritating than to be dismissed by an academic or author who thinks their degree or books written provide them with omnipotent ability to know everything they need in order to criticize security. As I've stated before, you're probably extremely smart in your area of expertise. This does not lend itself to transference into what I've done for 14 years. Sorry. But that's the truth. Again, I don't know a whole lot and there are guys in my field who are far more impressive than me. That being said, read this and #2.

- You say tomato and I say TOH-MAH-TO. Same difference. No, it's not the same. In security, certain terms do matter. They really do. For example, I had a very good conversation with a national security pundit I follow on Twitter, Joshua Foust. Joshua is smart when it comes to matters of national security and almost ties John Schindler in trolls except Joshua doesn't have a parody account yet and his and John's tweets are thought-provoking. That being said, our discussion this morning was about the efficacy of passport revocations. Joshua intimated revocations made jihadi terrorists stateless people. I find that most people confuse revocation of passports with revocation of citizenship. The two sound the same but are vastly different both in mechanics and impact. However, because they sound the same they are often confused. We saw this when Snowden's passport was revoked. People claimed he had been stripped of his citizenship, although he never formally renounced his citizenship nor did Congress or the President revoke it. In fact, the passport revocation is nothing more than a travel restriction. You're allowed to travel to other countries as long as your country provides you with a valid passport. If your country revokes your passport, you're no longer able to travel and can only come back to your home country.
Joshua would later admit the semantics were different and we both agreed there were mechanisms already in place with respect to fugitive warrants and the Foreign Terrorist Organization designation. Neither, from my limited knowledge, have been integrated when it comes to jihadi foreign fighters. Something, I'm sure the President and other leaders are seeking to change because the inherent value of Western foreign fighters for groups like the Islamic State is their passports. Western travel documents can gain you access to a variety of countries, if they're not revoked or cancelled. - I could take down security anywhere and I could break in there if I wanted to. Okay, that sounds very cool. I'm sure you could. However, taking down an unarmed security guard because he's 75 years old with a bad limp is vastly different than being faster than his radio and being tougher than the eight burly deputies who will respond. You might also be able to break into a facility. That's also great and amazing. However, keep this in mind - sometimes breaking into a facility has more to do with luck rather than skill or technical acumen - remember one of the latest White House fence-jumpers was a toddler. In other words, the sun shines on a dog's rear every now and then. You also may not be as lucky as you think.
- OMG, this breach was the worst breach EVER!! Stop. Full-stop. Don't move. Breaches happen all over physical security for a variety of reasons. Some are preventable, sure. Some are not. Some occur in ways professionals never thought of. Some occur because the security manager and his/her stakeholders accepted too much risk. All I ask is that before you roll up a physical security breach as the worst ever, analyze not only the breach but the totality of circumstances. Some people are making a big deal about the recent White House fence-jumper who made his way "into the White House". I'll take a moment and explain why this is wrong.
Yes, the White House fence-jumper recently made his way to an inner layer of the mansion. Keep in mind what I said about layers. Here's something most critics won't acknowledge mostly out of ignorance. The doors, which I have pictured below, are actually an entrapment area. Wait. What? Yes, the North Portico doors are indeed an entrapment area. What does that mean? Simply put, the exterior doors remain unlocked so exterior personnel (security and non-security) can enter through them and gain access through the second set of doors which remain locked and more than likely, guarded by on-duty US Secret Service Uniformed Division personnel. In other words, someone or something would need to verify your credentials before allowing entrance into the interior.The diagram of the White House showing the doors.
The North Portico doors UNLOCKED. But do you see the doors behind them?
Scriven, how does this change the fact that he should have never gotten that close? It doesn't. However, it's always best to remember while this is the first time someone has made it to those doors, there have been other more egregious breaches. Thirty-three others, to be exact. Remember when the airplane crashed in the White House lawn? I digress. Did the USSS accept too much risk by keeping the doors unlocked? Sure, but I'm also aware these doors were probably unlocked more for convenience for certain non-USSS personnel. How do I know that? Because I've done something similar in a variety of security situations. So what does this little exercise tell us? First, it tells you I have entirely too much time on my hands and I spend a lot of time on Twitter. Second, it tell tells you exactly why layers exist and whether they function properly. In this case, a few layers were breached but the resource was secured by one. Third, a lot of people are making wild assumptions without having read the official report nor has there been an accurate articulation from which direction the jumper entered or whether he had been observed (my guess is he was). Also, some of these same people make all kinds of weird guesses about the nature of security at the White House based on rumor and what television and the movies convey. No, the President will not firing an RPG at multiple jumpers next time.
Finally, it teaches us the value of relativity and complexity - this was bad but was it the worst? It's all relative. Seriously, can you imagine managing the security of POTUS and his/her staff and guests AND the most iconic tourist attraction in the Western world? It poses some SERIOUS security challenges which are countered every single day, mostly with zero incidents. If this was the "worst", then the Secret Service did an excellent job of containing the threat. - Security is pretty simple. I can't even.
- The Israelis do it better.
Israel has an entirely different security landscape than we do. It's also key to remember their adversaries surround them.
— Scriven King (@scrivenlking) September 20, 2014
Saturday, July 5, 2014
INFOGRAPH: What Happens to A Social Media When The User Dies
| Source: http://kupeesh.com/social/even-friends-wont-miss-facebook-plans-eulogize-die/ |
In my current occupation, as an investigator, most of my day is spent on social media. Much of that time is used figuring out who the account belongs to in order to make contact with the user for a case I'm working on. In security, we're often monitoring social media to gain some insight on kinetic events in our areas of operation. In either case, we run the risk of finding out the users of theses accounts being dead with little information given as to who may be using the account in their stead. I found this infograph here and sharing it on this space to help other practitioners.
Monday, June 23, 2014
OPINION: 10 Simple Rules Every Security Professional On Social Media Should Think About
Social media can be a great thing at times. It can connect you with other professionals, allow you to sound off on things in our industry, advertise your services, and even give you new insight into security matters. However, it can also be a very dangerous tool. Countless times, I've seen security professionals realize this inherent truth much too late. In every social interaction, there is an implied trust with our fellow netizens they will abide by certain unspoken "rules". Often, they do but more than often, they do not. I'd like to share a few rules that can help mitigate the risks associated with combining your personal and professional social media personas.
- Be humble and listen to everyone's opinion. There seems to be a rash of security professionals who believe the best way to interact with those who disagree with them is to be brash and rude regardless of the interaction. Sometimes, it calls for being a bit brash and rude. However, I find it often does not. Don't make being adversarial a part of who you are on social media. You could potential "scare away" potential clients or employers. Don't be "that" guy. Seriously. If you don't want discourse, then social media is not the place for you. Chances are just because you're awesome in what you know doesn't mean you're awesome in all things you claim to know. Sometimes, other folks have legit ideas we can learn from. You don't always have to be right. A simple "I never thought of it that way" goes a long way.
- Keep your "circle" small. A while back, I went to "private" on all of my social media accounts. Why? Am I talking secret stuff I don't want others to know? No. I just realized how much better my social media experience is by keeping my audience relatively small. Think of it like how you rate schools based on student-to-teacher ratios. Do you really want to have to interact with 90,000 people you don't know? Also, by keeping your "circle" small, you pick the people you want to interact with. There's a danger here, though. By being selective, you run the risk of limiting the amount of data you receive and it can enable subjectivity to some extent. With that being said, I'll add my next rule.
- Interact with people who provide value and not an ego boost. When I went "private", I noticed I was far more selective and I tended to interact with people who "liked" my comments less and interacted more. There's a trap by having loads of people "like" everything you post. It can lull you into a false sense of security that you're a "big deal" and immune to legitimate criticism. Remember, this is the Internet. Just because you say awesome things does not mean people think you're awesome. You will make people upset sometimes. That's life. Some attacks will be personal. That is also life. Deal with it. My mother provided me with the best sage advice I've ever heard and will never forget - "Not everyone that smiles at you is your friend and not everyone who frowns at you is your enemy."
- Don't say or do anything on social media you can't tell your mother or boss about. Seriously, you can limit half the drama that comes your way by just abiding by this simple rule. More professionals get involved in more drama online than they should because they forgot this. What does this mean? Don't write checks with your status updates your career and personal life can't cash.
- Keep it real. I've written in the past about "experts" and how often it is easy to confuse real expertise with implied expertise. If you're really knowledgeable about something, feel free to talk about it like you do. If you're not, then take it easy and try to "stay in your lane". Many people find themselves in trouble when they forget to do this. Why? Everyone wants to be popular on social media and you don't get to be popular by staying in your lane all the time. Remember what I said about getting too many followers and "likes". Again, don't be "that" guy. When I'm talking to people on social media, I try my hardest to be upfront about what I know based on my experiences and from other sources. If you follow me on social media, you'll often read me telling people what's in my lane and what is not. I find when I do that, I receive much better interaction with professionals and I learn quite a bit more than I preach.
- Don't make your social media persona to be something you are not. The downfall of many professionals on social media can be traced back to forgetting this rule. Quite a few security practitioners seem to believe in order to have value, they have to inflate who they are or what they've done in the past. More often than not, they're found out and revealed without prejudice. You don't have to fake a degree or have an awesome job title to provide value in your social media interactions. I'm more impressed by a person who is totally honest about being a janitor and knows a lot on a topic versus a janitor who pretends to be an "expert" security "guru. As I always say, "Game recognizes game."
- Use your manners. My advice to son is always, "I get more from pleases and thank-yous than I have ever gotten with a frown on my face." A simple "Thank you for the discourse" or an apologetic private message for an overly snippy comment has provided me with more value than my stubborness to concede a point ever has. With that in mind, as with everywhere you go in life, there will always be jerks. Try not to be one of them if you don't have to. Sometimes, a situation online may call for you to be one. I suggest resisting the temptation to do so and simply either ignore the other party or "block" them. This is the Internet and there are tools available wherein you can choose to be a jerk or not. At one point, my mother was a preacher's wife which is position replete with jealousy. She always told me, after an encounter with someone who she knew didn't like her, "Baby, sometimes, you gotta kill them with kindness."
- Some things are better said in-person. This is too easy to explain. Keep private things as private as you can because once it leaves your computer, you have lost complete control of it. If I'm in charge of human resources at a company you applied to or I'm a prospective client and I noticed your social media accounts are chock full of indiscretion, you're probably not a person I want to hire and for good reason. Whatever your intent was will not matter to someone who decides your fate with the click of button without having to ever talk to you.
- Never trust people to keep things private online. Salient advice I received from a friend once - "This is the Internet, nothing is as it appears." People are inherently untrustworthy. Why? Because they can always make disadvantageous decisions regarding you online without your knowledge and consent. There is very little you can do about this except following this rule. As the old adage from hip-hop goes, "Never trust a big butt and a smile."
- You don't have to be first to speak during a crisis to have value. The first time I became popular on social media was during Christopher Dorner's rampage through Los Angeles. I made a few points which were re-shared a lot. After that, it seemed like every other crisis, I was being called on to give my opinion. Not too long after that, I did some introspective thinking and realized I was being wasn't always being called on to give my opinion or insight - I was seeking it out. I had fallen into the trap. Why is this bad? The reason I took the time to think on this topic was I noticed I was sharing incorrect and highly subjective information. In other words, I was misinforming people. My "circle" was kind and quietly called me on some of it. Here's what I learned: Being first, often, means being first with the wrong information and relying on firsthand accounts. Anyone involved in the intelligence community will tell you how this leads to a degradation of analysis and eventual disregard of the analyst responsible. Take your time and give your insight when it's helpful.
Saturday, April 26, 2014
OPINION: Why Does It Suck To Think Like A Good Guy In Security
Day after day, on social media and elsewhere on the Internet, there are lots of folks who are seemingly shocked every time a bad guy shows up and acts like a bad guy. Seriously, how many times have you read or seen "I can't believe Suspect A was able to murder all of those people" or "If only they (security) did XYZ like I thought of during a conversation with my veterinarian who may have been in the military, that bad thing wouldn't have happened"? I see it quite a bit and frankly, I've decided it may be time to finally add my .02 about it.
Those of us in security who have spent some time studying "the threat" (insert whatever scary bad guy you're dealing with) understand what few who haven't studied it don't. No matter how awesome your protective measures are, they do little to mitigate (and certainly not "prevent") the attacker unless you start thinking a bit like they do. Herein lies the fatal flaw of most "white hats" and even some "grey hats".
- You think of attacks in ways that you would conduct them. No offense but if you're protecting yourself against robbers but know relatively little of them, you may be looking to deploy solutions which don't work against that threat. One of the most painful things any security professional can hear when doing a site survey with a client from the client is "If I were the bad guy, this is how I would do it." More often than not, it is not how the bad guys would attack. Think security cameras in homes. Most people will deploy a camera at home with the thought the camera provides an extra layer of protection when in fact it doesn't. I have known several victims of home invasions who either had cameras installed or had an alarm sign out front. These are two commonly deployed deterrence tools that we know don't work. Instead, focus on the problem as if the bad guy would ignore the deterrence measures (because he will because we have little proof he won't) and proceed with the attack and use things like cameras as after-incident mitigation tools to catch the perpetrator later.
- You think of your threat as one-dimensional. Most good guys see their threat based on commonly accepted precepts of what the threat is and how he has attacked in the past. Just because the bad guy only hit you or the other guy using one vector doesn't mean he won't try something different later. A great example of this is 9/11. Prior to the second World Trade Center attack, there were common beliefs that terrorists were only capable of performing certain kinds of attacks. What no factored in was changing realistic threat capabilities. In other words, we assumed the threat wasn't evolutionary in his tactics. Seriously, who could've imagine having to protect a building against two near-simultaneous aircraft crashes? Perhaps we could have had we accepted the idea that as we change so does the threat.
- You think the threat is omnipotent and omnipresent. It's easy to get caught up in the hype of a threat. I do it sometimes. This is a natural defense mechanism after an attack has occurred. Why? No one likes to have their vulnerabilities exposed. After every mass shooting or act of violence that makes the news, we assume every venue that is like the one that was attacked is also vulnerable and being selected as the "next" target for another perpetrator.
I remember fondly working on 9/11 on a small Air Force base on a perimeter patrol. What I recall the most are the initial attitudes people had of al Qaeda. We believed this one attack displayed a level of sophistication unseen by them before on US soil could be replicated on a massive scale. Every Muslim, ignorantly, was assumed to be a sleeper agent waiting for cues from "Muslim HQ" to attack us wherever and however they chose. The months and years ahead showed how far from the truth that was. Imagine how many countless resources were expended before we realized the fallacy behind this assumption. - You think your attacker "chose" you for a variety of reasons he didn't. People almost always assume an attacker chose to attack them or others for reasons they didn't. Rape is commonly thought to be a crime of lust because good people believe sex is the only reason you rape because it's the end-result. However, most criminologists and psychologists would agree rape is a crime of power. I would argue the majority of crime takes place for this very reason. Terrorism occurs because of this as does murder (what's more powerful than ridding yourself of someone permanently), drug dealing, fraud, and a host of other crimes. You're either fighting to obtain it (i.e. steal it from someone else) or committing crime to become more powerful. This confusion could possibly explain why most crime "prevention" measures based on policy fail at alarming rates - we're clueless on what truly motivates people to attack us.
- You assume because you haven't seen the threat, he must not exist. Whether we see the threat or not, we should never assume he does not exist. While the threat can't be everywhere every time, the threat can still be very much. Never assume the absence of threat means he or she isn't going to show. You still need to adequately protect your assets as if today is the day you're going to be attacked. Remember, the attacker chooses the time of attack. You choose how well-prepared you'll be when it happens.
- Study your adversary. Seriously, pour over any open source intelligence you can on your threat. Read the paper and look for crime stories. Pick up a police report or two on similar venues like yours. I'll leave how you conduct your research to you. Just do it. Stop assuming blindly how the attack will go down or even who your adversary is.
- Consider hiring folks who can think like attackers. I'm not saying you hire criminals but red teams hire specialists who can mimic attackers. Choose folks from a variety of backgrounds to round out your security team. By the way, by "background", I'm not talking education. I mean pick a team with a variety of specialists.
- Test your systems with exercises. The only way you're going to learn is by testing how well your security program holds up against an actual attack. Consider doing this with little to no notice and have an after-action or "hot-wash" debriefing with your red team and affected staff right away. Finally, fix the vulnerabilities as soon as possible.
- Reward outside the box thinking. When I was a young boy, I recall my fondest memories were playing games like "hide-and-go-seek" with my friends. The guys who were the most creative were the best at this game. Why? Because they were unpredictable. I'll leave how you choose to reward these folks on your own. Just do it.
Thursday, April 24, 2014
PHOTO: Fake Cameras Provide Fake Protection
I can't even begin to tell you how many times I run into stores that have decoy cameras in lieu of real cameras. I also can't tell you how many countless times these same stores get robbed. Buying a decoy camera, in my opinion, are invitations for criminals. This is not to say most criminals can't tell the difference between fake and real. This is to say that many of these businesses and homes that utilize decoy cameras don't quite get what kind of mitigators they need to adequately protect themselves and their assets.
The added statistic at the bottom of this photograph is especially troubling because it dupes customers into believing they have added another layer of "security". This is correct in some respects. Remember what I said about "security" being a goal and less of an action? The problem lies in exactly the same place issues of semantics in security are - it relies on data that is either incomplete and more than likely, irrelevant to their protection needs.
We all know cameras serve a variety of purposes other than video surveillance. We also understand some vendors and property owners either have poor tools or are so under-trained they may as well not have a camera. However, when an incident happens, the last thing property owners want to tell the police and insurance companies (worse yet, a jury in a civil liability trial) is they thought a decoy or non-operative camera offered better protection.
If you're a property owner and considering one of these decoys, turn around and invest in a camera system you will monitor and maintain. If you're a pro, call these out and the dangers behind using them.
Tuesday, April 22, 2014
The Semantics of Security - The Great Enabler of Security Ignorance
One of the toughest and most insightful lessons I learned came during a conversation with a good military buddy about why English is such a difficult language to learn. "You never mean the things you say. You say you "love" your car in Spanish, it means you love it like family. It's as if you use the words so much they lose their actual meaning." I was a bit taken aback by this. No one had ever explained the issue of semantics so eloquently before to me.
This same thing happens in security and explains what makes it so difficult for so many professionals and lay-people to be able to comprehend it. The following are great examples:
- Prevention versus mitigation. Prevention is defined by Websters as "the action of stopping something from happening or arising." Mitigation is defined by Websters as "the action of reducing the severity, seriousness, or painfulness of something." The words mean something completely different from the other, yet are used interchangeably. In security, getting these two words wrong can mean the difference between a loss of life (yours or an innocent) and victory over an attacker. Having lofty goals of prevention through methods and measures seldom tested with actual bad actors, often leads to failure when they do show up. However, having sound mitigators in place should they attack, could save both life and property and result in the consequential capture of your bad actor. The decision to stop his or her actions is totally dependent upon his or her decisions and plans before and during the attack. Your measures could help persuade them not to attack but I would hardly call this prevention without more quantifiable evidence.
- Vulnerability assessment versus reconnaissance. A vulnerability assessment is a process which entails analyzing a client's assets to determine likely avenues of approach for attackers. It could involve talking to stakeholders, physical walkthroughs of the assets, imagery analysis, and red-team exercises. Reconnaissance is a process which entails some covert surveillance resulting in a report to the target's adversary to support a plan of attack on the target. These terms are often confused because people assume one means the other. Typically, bad actors do recon and friendly agents do vulnerability assessments. The latter could use the former as part of a red-team exercise or even as part of a walkthrough. However, the methods by which either is done are very different. Keeping this in mind prevents amateurs from thinking by doing reconnaissance, they are in some way doing a complete vulnerability assessment.
- Security versus protection. It grates my nerves to hear people say they are "doing security". I find most people have no true understanding of what the term means and are therefore, ill-suited for and failing miserable at the task they think they are doing. As I've discussed before, security is a mental construct wherein our protective measures are adequate enough in our minds to mitigate bad actors and their attacks to make us feel secure. It's a subjective term but more of a goal and less of an action than anything else. Protection is what we do to make the environment secure enough to assuage our fears of a possible attack.
- Arrested versus detained. It took me a while to get used to this. They both sound like they should mean the same thing but they do not. Ask anyone who has ever been arrested. Being arrested has an element of detention but it isn't the totality of the action. You can be detained without being arrested. While this may sound like an issue of semantics, ask your legal counsel to explain what happens in security when you confuse your ability to detain versus your arrest powers.
- OPSEC. OPSEC is one of the latest buzzwords to come into the modern security lexicon. Everyone believes they do it but few actually do to include me at times. Seriously, everyone on social media who is in our industry seems to have a burner cell phone number, 10 fake IDs, wall safes for their wall safes for the wall safes with their encrypted USB, uses TOR to hide from the NSA (as if), etc. The first rule of being good at operations security is to shut up about OPSEC. What's the first thing people do when they think they've done something awesome with respect to OPSEC? They tweet about it on a source they don't own with people they don't know or could vet with any realistic degree of certainty, using communication they know very little about on the Internet which was created by some of their adversaries who have actively engaged in intelligence operations here since its inception. So if so few get it, why do they think they've adequately protected themselves? See the difference between prevention and mitigation.
- Intelligence versus information. I often hear professionals claim they have "intelligence" on adversary, when in fact they don't. Most often they have only raw information they haven't vetted or analyzed. These colleagues suffer from the correlation paradigm where they mistakenly conclude correlating or parallel information to an event is the cause. In the analyst world, this is called "confirmation bias". You believe the information because it confirms what you believe. Intelligence is the product of taking that raw information, vetting its source, comparing and contrasting that data against previous data and assumptions, peer reviews, and a final reporting of that information with an analysis centered on critical thinking. A newspaper article in and of itself is not intelligence because it says something we already thought was true. That would be akin to treating Weekly World News' stories on aliens consulting a still-alive JFK on Elvis' newly proposed welcome-back world tour as intelligence because you're an Elvis-loving, conspiracy theorist who believes you're an alien-abductee.
- Guard versus officer. I'm sure to stir up something here. Let me clarify: there is NOTHING wrong with being a "guard". However, traditionally, that word has gotten a bad reputation. Think "mall security guard". These guys can be awesome professionals but the title does tend to minimize the extraordinary amount of work it takes to protect the thousands of mall patrons and mall assets against a variety of threats daily. It also does little to note the authority which enables them to perform certain legal actions against those threats such as trespass advisements and in some cases, arrests. "Officer" denotes they are an extension management and not merely someone who stands a post. They represent the extent to which managers are willing to go to protect their assets and their customers.
Recently, during a discussion with another friend from the military, I recalled a conversation about semantics with a person who worked in what was commonly referred to as the "chow hall". One day, I inquired why the name "chow hall" was such an insult to him. He explained "Do you guard planes or do you protect assets vital to national security? I don't cook chow. I cook meals which are nutritious as per my training. We're both professionals. I know people mean no harm but that term implies my food and what I do as a professional are sub-par and unworthy of a professional title, when that's not true." Vets, I hear the snickering. Stop laughing. But he had a point. One that wasn't lost on me.
How your customers see a "guard":
An image the term "security officer" typically conveys:
- OSINT versus unclassified. I'm a huge supporter of open source intelligence (OSINT). This entails gathering intelligence from a variety of non-covert channels. This could include public radio, news broadcasts, social media, etc. I have noticed this word used to excuse what I believe to be gross violations of protecting classified or sensitive information. Let me explain. I certainly understand OSINT by its nature can come from unclassified channels. However, I also realize it does not negate professionals from their responsibility not to divulge information coupled with their "insider perspective" which may be tactically advantageous to an adversary. You can observe this lack of professionalism best on social media, during a critical incident. There's seems to be a pandemic of sorts when these incidents happen which encourages its victims to feed their egos by talking endlessly about their highly sensitive "insider knowledge". I, once, observed someone who is widely considered an "expert" tweet the locations of responding forces to a major hostage situation. Another person tweeted security measures at a base they just left. Sure, none of this was classified because it came from a radio scanner and personal experience. It was, nonetheless, highly sensitive and could have placed lives at risk, if the adversary had intercepted these messages. In the physical security, once sensitive information is compromised, we only have a precious, small amount of time to deploy mitigators. As I'm often say during these events, "Don't let your ego and mouth write checks your a-- can't afford to cash with someone else's collateral."
We've moved a table to barricade the door into this room. pic.twitter.com/FXj33EynxE
— Federico Barillas S. (@fgbarillas) October 3, 2013 - Active shooter versus mass killing. The best way to explain this is simply stating not every active shooter kills anyone and not every mass killing involves a gun. Yet, whether because of politics or hype, professionals and laymen still confuse these two. This may seem meaningless until you realize how information is gathered to study these two distinct events and the influence those studies have on policy.
- Security theater versus threat mitigation. Look, folks, as professionals, we realize not every threat is going to attack us. We also get some of our measures are extreme. I'm certainly NOT trying to justify any abuses of authority or trust. That being said, just because you don't see the "boogey-man" doesn't mean he's not there. Does this mean security should have authority to do cavity searches on everyone? No. But it doesn't mean because that's extreme that someone isn't trying to do you harm. Do some threats get blown out of proportion? You bet. A vigilant public and other professionals are awesome checks against overreach, though. As every threat isn't realistic, every threat mitigator isn't security theater. We'd all do well keeping this in mind.
There are a load of others I would add but I feel as though this list does a great job of illustrating the power of words in our industry. Please use them carefully. If you have more, let me know.
Subscribe to:
Posts (Atom)

.jpg)
.jpg)
.jpg)
.jpg)



